Privileged Access Management
Netwrix Privilege Secure
Netwrix is a company specializing in cybersecurity software. More than 13,000 organizations worldwide already use Netwrix solutions. Founded in 2006, the company has received more than 150 industry awards and has been included in the Inc. 5000 and Deloitte Technology Fast 500 lists. The company is headquartered in Texas, USA.
Netwrix Privilege Secure is a solution for controlling and managing privileged access.

Get Netwrix Privilege Secure Demo
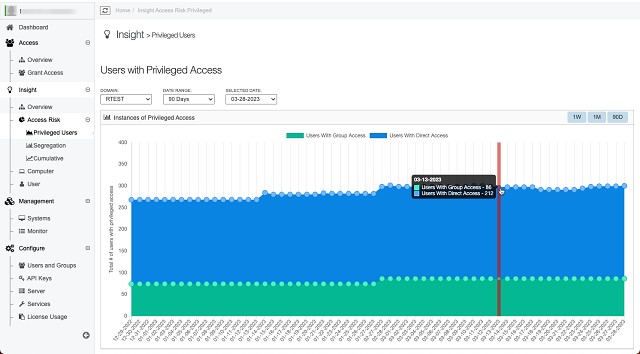
Continuous scanning identifies unmanaged or unknown privileged accounts. This helps to stop the attack from expanding within the organization, as unnecessary accounts are removed and no longer a vulnerability.
Identify weak areas in minutes
With Privilege Secure, tens of thousands of endpoints can be scanned to identify potential entry points for attackers, and continuous scanning helps control the growth of privileged accounts.
Implementation of zero standing privileges
Removes unnecessary administrative accounts from all endpoints with a single click, reducing the risk of malware installations or changes to critical security settings.
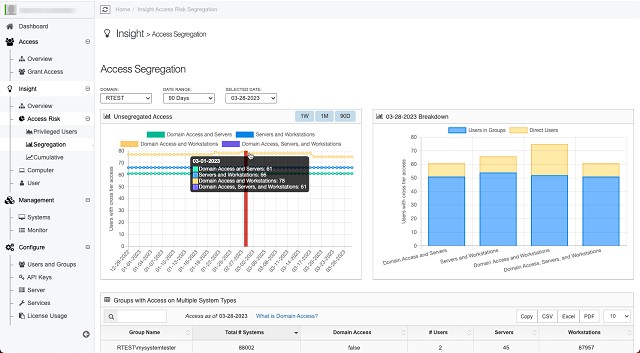
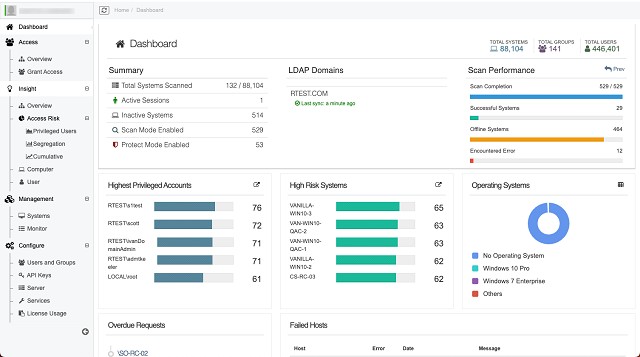
Attack surface visibility
Visualize, analyze, and manage your environment with dashboards designed for executives and IT professionals. Overview of all accounts and activities to have situational awareness of privileged activities.
Reduce security risk with zero privilege, secure credentials, and detailed session monitoring.
Manage standing privileges
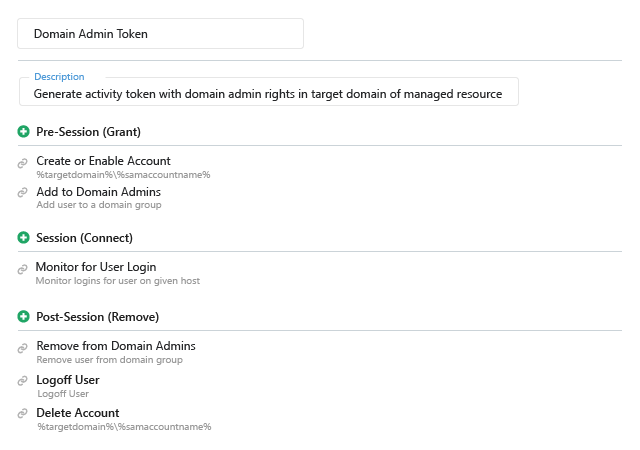
Netwrix Privilege Secure creates and deactivates accounts on a per-session basis, leaving attackers with no accounts to compromise. Thanks to Netwrix Privilege Secure’s orchestration mechanism, all privileged accounts on all systems are temporary.
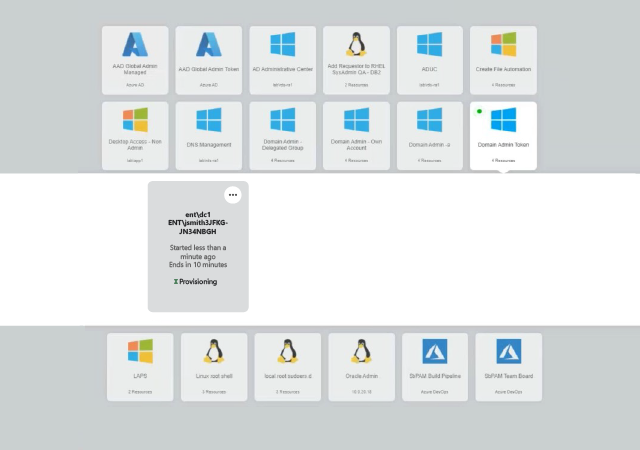
Flexible access management
Facilitate the work of specialists with intuitive and easy-to-use workflows. Dynamic access control to resources and credentials.
Visibility of privileged sessions
With full real-time monitoring, session recording, and keystroke analysis, malicious activity can be quickly detected and eliminated.
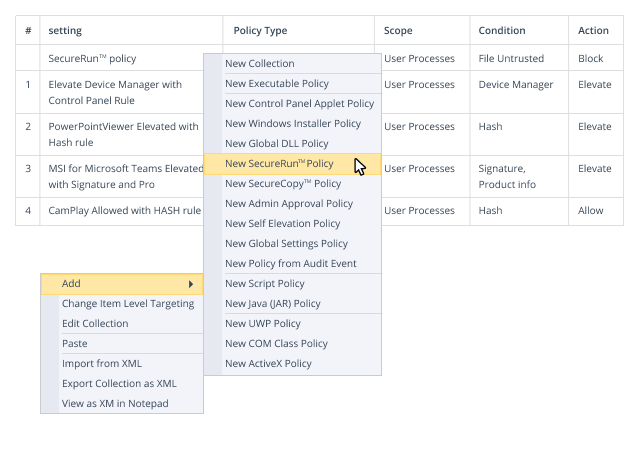
Prevent the risk of malware, ransomware, and regulatory compliance by delegating only the permissions required by standard users, not local administrator rights.
Protect Windows endpoints from ransomware and malicious changes
Ability to prevent users from installing unknown software and control how they use removable storage. Restrictions on changing software settings. Control over the correct configuration and deployment of group policies.
Increase productivity
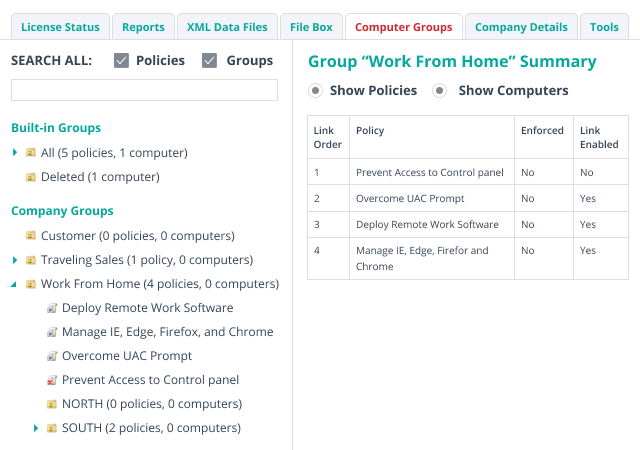
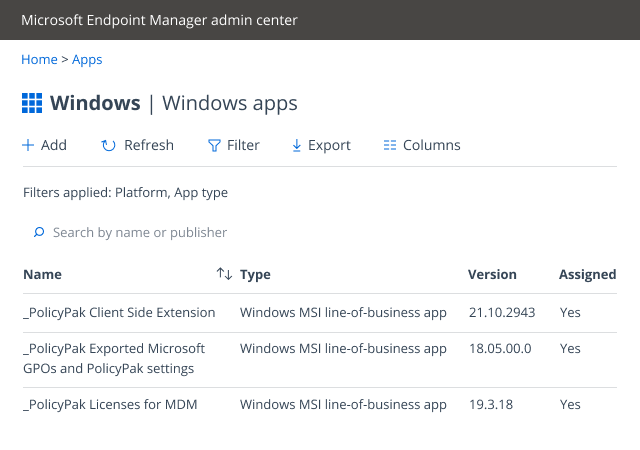
Deploy software and custom OS settings to any Windows endpoint, whether it’s domain-joined, MDM-registered, or virtual. Consolidate Group Policy Objects (GPOs), automate scripts, simplify VPN management, and more.
Modernize your desktop environment
Manage and secure your on-premises, hybrid, or remote workspace with a single solution.
The main features

Removal of standing privileges
Reducing the attack surface by removing standing privileges. Instead, you should create temporary accounts with access sufficient to perform the task at hand and delete them when the work is completed.

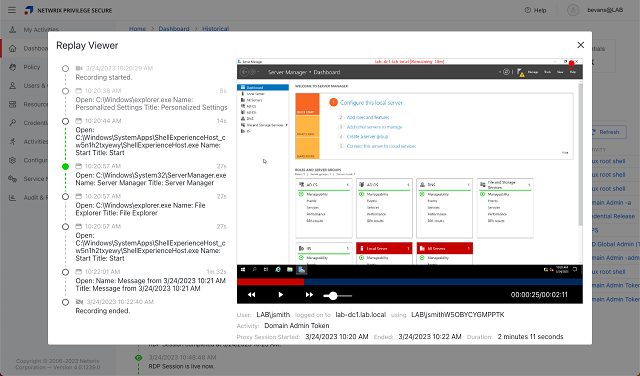
Real-time session monitoring
Improve reporting by tracking all administrator actions in real time across multiple IT systems. Monitor sessions and immediately stop suspicious activity.

Protect your service account
Secure these accounts with process change notifications and the ability to immediately stop and roll back any unwanted changes.

Assistance in incident investigations
Ability to view and search for video recordings of completed sessions. Further use of the information found to provide convincing evidence during an audit.

Fast audit
With Netwrix Privilege Secure, experts will be able to quickly prepare detailed reports on each privileged account, its sessions, as well as what actions took place during the activity of this account and whether any local groups or critical files were changed.

Integration with storage
Integrate Netwrix Privilege Secure into your current company’s storage, or use Netwrix storage to store any privileged credentials.

Protecting local administrator accounts
Improve local administrator account security while maintaining operational efficiency by integrating Netwrix Privilege Secure with LAPS (Local Administrator Password Solution).

Facilitate existing workflows
Netwrix Privilege Secure can be safely and quickly integrated with existing internal and third-party applications.
Improved threat detection
Strengthening the threat detection mechanism by being able to send logs of privileged activity to the company’s SIEM, where they are correlated with information from other systems.

Control of privileged users
Ensure compliance and improve security by regularly checking the legitimacy of each user’s privileges.

Automation
Automatically enabling/disabling RDP and cleansing Kerberos tokens helps to further reduce security risks.

Authorization check
Verify that all privileged actions are legitimate and performed by a trusted user by approving or denying requests for privileged access.

Zero Trust
Verify identity data by applying contextual multifactor authentication (MFA) every time an administrator initiates a privileged session.

Protect database administrator accounts
Supports identity management and privilege orchestration for MS SQL Server and Oracle.

Detailed statistics
Access to ready-made and customized reports. Easy to use thanks to the intuitive dashboard.

Session tracking
All SSH and RDP keystrokes and local command execution are recorded, and detailed metadata search is available for both active sessions and recorded sessions.

Detect unmanaged accounts
For each supported platform, the built-in scanner contains a list of all domain and local accounts with the corresponding privileges. New controls make it easier to identify and manage unmanaged privileged accounts.