Author: Julia Grits, Netwrix Brand Manager
Privileged Access Management (PAM) has already become a core component of modern cybersecurity, enabling organizations to control access to critical resources by users with elevated privileges. The PAM market continues to grow — and this is not just a trend but a direct response to real data protection challenges.
Exponential market growth
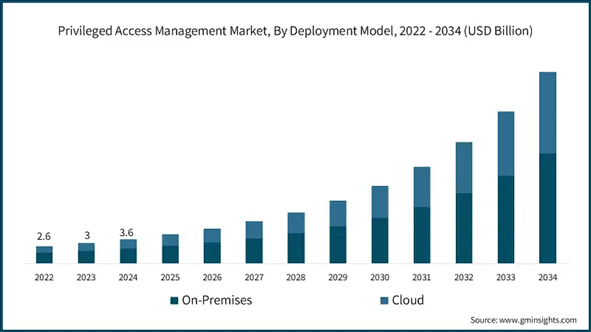
In 2024, the global PAM market was valued at approximately USD 3.6 billion. In 2025, it reached USD 4.44 billion, with the BFSI (Banking, Financial Services, and Insurance) sector accounting for around 30% of demand.
By 2034, the market is projected to grow to nearly USD 30 billion, with an average annual growth rate exceeding 23%.
This growth is driven not only by technological needs, but also by regulatory requirements (GDPR, HIPAA, PCI DSS) and the ongoing shift toward hybrid and cloud-based infrastructures.
Let’s look at the numbers:

Key drivers of PAM adoption
1. IT infrastructure transformation toward cloud services and remote work
Organizations are increasingly migrating applications and infrastructure to the cloud. This naturally drives demand for Privileged Access Management tools, which are critical for securing privileged access in multi-cloud and hybrid environments.
2. Increased risks related to compromised credentials
The growing number of credential-based attacks makes privileged access one of the primary risk vectors. According to Netwrix, in 2025 credential theft incidents increased by nearly 800%, while ransomware attacks grew by 179%. This significantly amplifies the need for centralized control, monitoring, and privilege limitation.
3. Compliance with Zero Trust principles and cybersecurity insurance requirements
Modern security models, including Zero Trust, require strict control of privileged access based on least-privilege principles and just-in-time access. Additionally, insurance providers increasingly mandate PAM controls as a prerequisite for cyber insurance coverage or reduced risk premiums.
4. Diversity of privileged accounts
Privileged accounts extend far beyond traditional administrators. They include service accounts, cloud service identities, application accounts, and more. Each type has its own access levels, permissions, and lifecycle requirements. Managing this “zoo” of accounts can be a significant challenge.
Additional operational challenges organizations face:
- integration with legacy systems and heterogeneous environments
- high initial deployment costs
- administrative overhead
How to select and test a PAM solution
When choosing a PAM solution, it is essential to focus not only on features but also on real-world applicability. Key steps include:
- conducting a Proof of Concept (PoC) using real operational scenarios
- validating just-in-time access, automatic privilege revocation, session visibility, and depth of integration with existing tools
- avoiding solutions that rely on static password vaults, overly complex workflows, or weak support for cloud-native accounts
PAM evaluation should be based on real use cases and the solution’s ability to scale alongside the infrastructure.
Key PAM trends
The modern PAM market is shaped by the following trends:
- replacing permanent privileges with dynamic access
- compliance-driven monitoring and logging of privileged accounts
- deeper integration of PAM with Zero Trust models and access automation
- increasing focus on cloud and SaaS architectures, although on-premises PAM deployments still dominate
In 2024, the on-premises segment accounted for 61% of the market and is projected to exceed USD 16.1 billion by 2034, maintaining a strong position. Organizations with on-prem infrastructure continue to prioritize strengthening internal network security.
As cyber threats evolve, enterprises are investing in more robust access control solutions to protect sensitive data and mission-critical systems from unauthorized access. Demand is growing for solutions that provide granular visibility, enforce least-privilege policies, and ensure compliance with both internal and external regulations.
And of course about AI 🙄
As the cybersecurity market continues to leverage advances in artificial intelligence, PAM is increasingly shaped by automation. Management capabilities will include AI-driven assistance and additional automated processes, expanding coverage and efficiency.
Potentially, these solutions will offer stronger protection for privileged accounts by leveraging advanced machine learning techniques and automated response mechanisms.
Conclusion (actually short)
Privileged Access Management is no longer an optional security layer — it is a foundational control that reduces risks associated with privileged access and strengthens organizational cyber resilience. In today’s environment of constantly evolving digital threats and distributed infrastructures, PAM is becoming a standard rather than an option.







