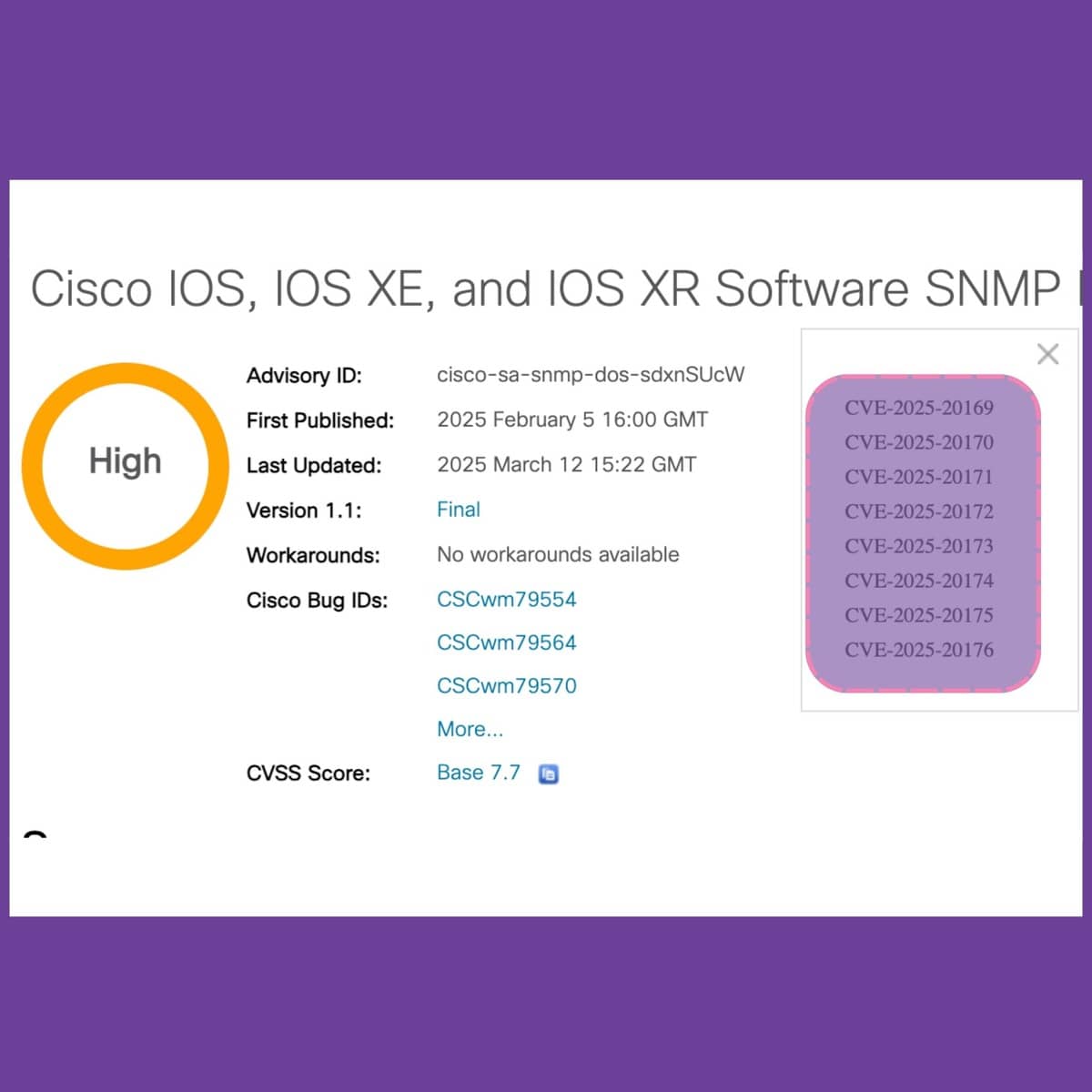
A total of eight Cisco vulnerabilities (CVE‑2025‑20169 to CVE‑2025‑20176) were initially released in the National Vulnerability Database (NVD) without corresponding CPE configurations. Due to the absence of CPE mappings, these vulnerabilities remained invisible to asset discovery systems and automated scanners that rely on CPE identifiers for detection. DeviceTotal closed this visibility gap by extracting the relevant firmware version—IOS 15.9(3)m3—directly from Cisco’s official security bulletin, allowing for accurate identification and timely mitigation. As a result, the customer was provided with comprehensive visibility and could carry out precise, timely remediation. The NVD eventually incorporated the missing CPE data in July—approximately four months after Cisco’s initial disclosure.
The DeviceTotal Difference
| Without DeviceTotal | With DeviceTotal |
| ⚠️ Vulnerabilities remained undetected due to absent CPE associations in NVD | ✅ All 8 CVEs correctly linked to affected Cisco firmware |
| ⚠️ Scanner output misrepresented the true security state | ✅ Firmware-level accuracy eliminated false positives |
| ⚠️ Heightened exposure due to unpatched security flaws | ✅ Remediation efforts aligned precisely with vendor advisories |
| ⚠️ Issues stayed hidden for four months owing to missing CPE data in NVD | ✅ Full visibility into device risk with daily updates, despite NVD’s delay |
The Security Oversight
- Device involved: Unspecified Cisco device running IOS 15.9(3)m3
- Data source used: NVD
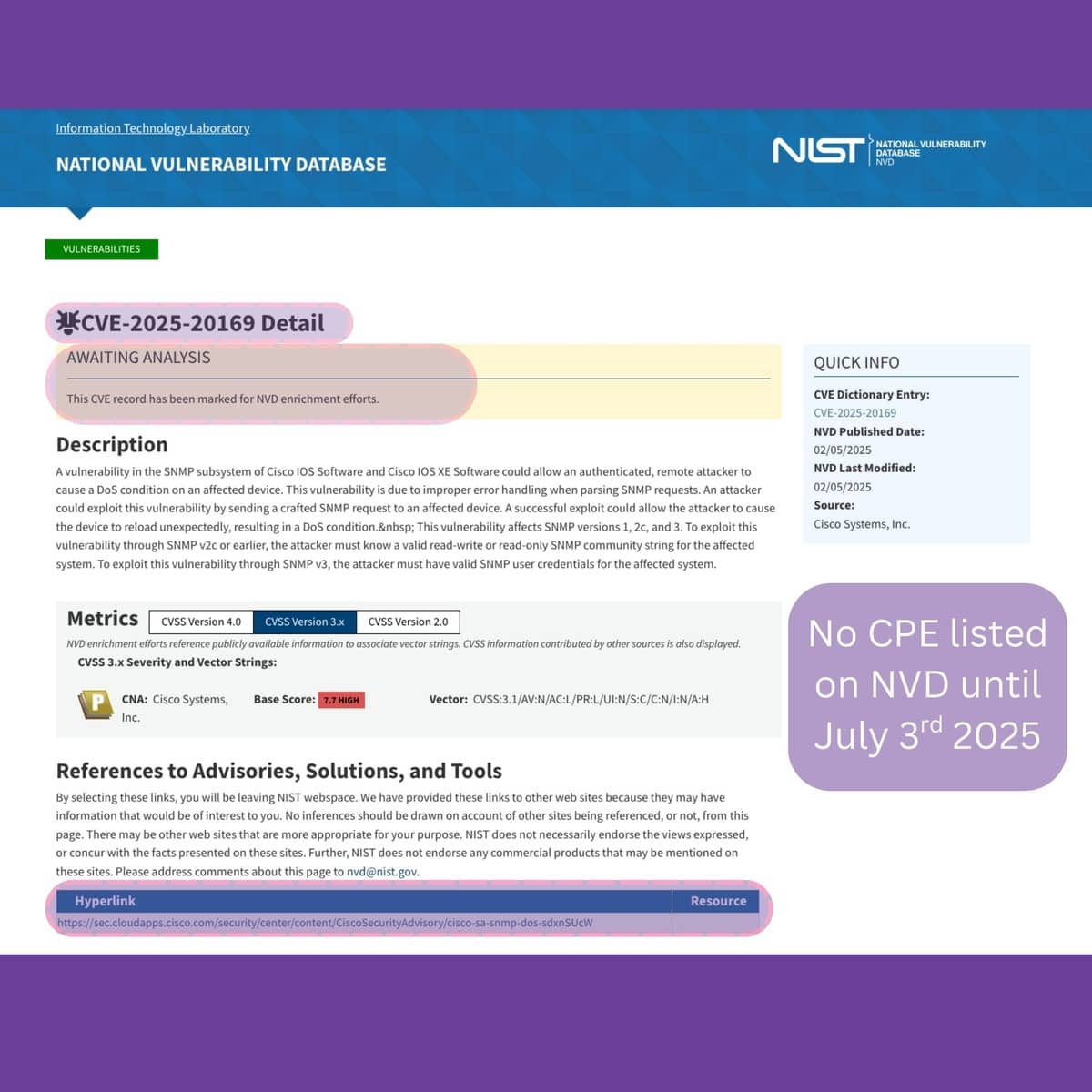
- Issue: Eight CVEs tied to Cisco SNMP DoS vulnerabilities were not associated with any CPE entries in the NVD until July 3, 2025, even though Cisco had published an advisory back in February of the same year.
- Clarification: Although the NVD did include a link to Cisco’s advisory, the absence of specific CPE identifiers meant that automated security tools were unable to detect the risk.
DeviceTotal’s Findings
DeviceTotal continuously monitors vendor security bulletins and does not depend exclusively on NVD product-to-vulnerability mappings. The platform parsed Cisco’s advisory directly to identify the impacted firmware versions and:
- Matched all eight CVEs to IOS 15.9(3)m3
- Enabled the customer to direct remediation only toward confirmed exposures
- Source: Cisco PSIRT
On July 3, almost four months following Cisco’s original disclosure, the NVD eventually amended its database to include the corresponding CPE identifiers.
Note: The example shown represents only one of the eight CVEs updated on that day. The remaining CVEs can be reviewed individually via the following links:
- CVE-2025-20170
- CVE-2025-20171
- CVE-2025-20172
- CVE-2025-20173
- CVE-2025-20174
- CVE-2025-20175
- CVE-2025-20176
Outcome
DeviceTotal brought to light vulnerabilities that tools relying solely on NVD data failed to identify. By supplementing the incomplete CPE information absent from the public CVE entries, DeviceTotal enabled the customer to:
- Detect all eight authentic SNMP DoS vulnerabilities affecting IOS 15.9(3)M3
- Patch proactively instead of operating under the false assumption of zero risk
- Demonstrate thorough due diligence during internal reviews and third-party audits, regardless of NVD’s initial oversight
- Eliminate the need for manual CPE lookups or custom scripts for securing Cisco devices
In essence, DeviceTotal transformed a hidden threat into a clearly defined and actionable remediation path.
Why This Is Critical
DeviceTotal’s advanced threat intelligence engine monitors far beyond NVD and incorporates:
- Official disclosures from vendors
- Vendors that do not publicly report vulnerabilities
- Zero-day intelligence
- Enriched proprietary and classified data feeds
This approach ensures broad-spectrum risk coverage through:
- Daily threat data updates
- Risk scoring tailored to firmware-specific exposures
- Comprehensive visibility across IoT, OT, network, and security hardware
- Clear mitigation strategies, even when NVD data is delayed or inaccurate







