In the oil and gas sector, each hour of operational downtime directly results in reduced production output and elevated compliance risk. Mission-critical OT assets, including Rockwell ControlLogix 5580 controllers, are widely deployed across refineries, pipeline infrastructure, and offshore production facilities.
When such devices operate on outdated firmware, even a single unaddressed vulnerability can trigger a chain of consequences, ranging from safety hazards and regulatory exposure to operational losses reaching millions of dollars.
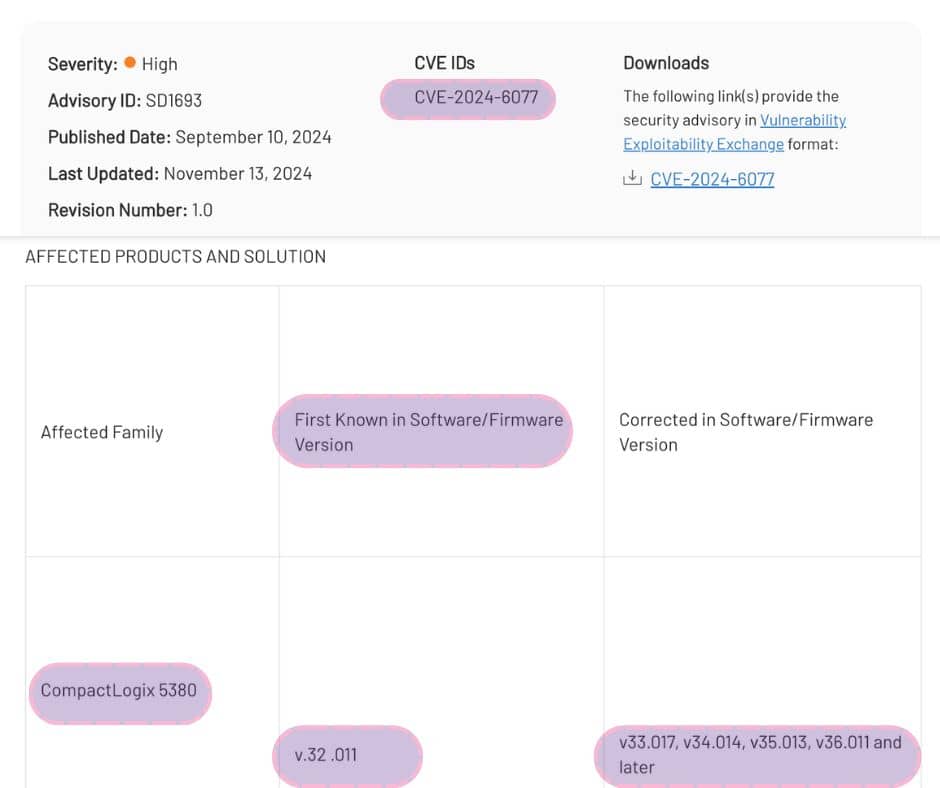
One documented instance involved firmware version 32.011. Rockwell’s official security advisory confirmed that this firmware version is affected by CVE-2024-6077. However, within public vulnerability databases, the issue was associated with GuardLogix rather than ControlLogix. For operators whose environments catalog assets under the ControlLogix classification, this discrepancy caused production controllers to appear non-vulnerable during scans, despite being affected.
The outcome was a large-scale false negative, creating a significant security gap and leaving critical infrastructure exposed.
| Without DeviceTotal | With DeviceTotal |
| ⚠️ Vulnerability not detected due to CPE mismatch | ✅ CVE-2024-6077 accurately associated with ControlLogix 5580 / firmware 32.011 |
| ⚠️ No clearly identified remediation guidance | ✅ Vendor-validated remediation path confirmed (resolved in later versions according to Rockwell SD1693) |
| ⚠️ Reporting that failed to meet compliance expectations and resulted in delayed patching | ✅ Daily risk scoring synchronized with official vendor disclosures |
| ⚠️ Dependence exclusively on NVD CPE data | ✅ Verifiable provenance supported by Rockwell SD1693 and corresponding NVD records |
The Security Gap
- Device in Operation: Rockwell ControlLogix 5580 (1756-L83E)
- Firmware Version: 32.011
- Search Source: NVD / traditional vulnerability scanner
- Result: CVE-2024-6077 — firmware version 32.011 was listed exclusively under the GuardLogix 5580 CPE and not under ControlLogix 5580. In the public database, version 33.011 was identified as the earliest affected release for the ControlLogix 5580 device family.
Within oil and gas OT environments, where assets are classified as ControlLogix, the vulnerability was not flagged. As a result, safety-critical systems were incorrectly reported as secure.

The Reality Identified by DeviceTotal
DeviceTotal correlated Rockwell’s official advisory with real-world asset intelligence:
- Vendor: Rockwell Automation
- Advisory Reference: Rockwell Security Advisory SD1693
- Impacted Device: ControlLogix 5580 (1756-L83E)
- Firmware: Initially affected in version 32.011, resolved in subsequent releases
- Status: Public vulnerability record published, but incorrectly mapped at the device level
- DeviceTotal Value: Consolidation of vendor-verified advisories and public vulnerability data, eliminating false negative conditions for ControlLogix assets deployed in oil and gas production networks.
Actionable Insights
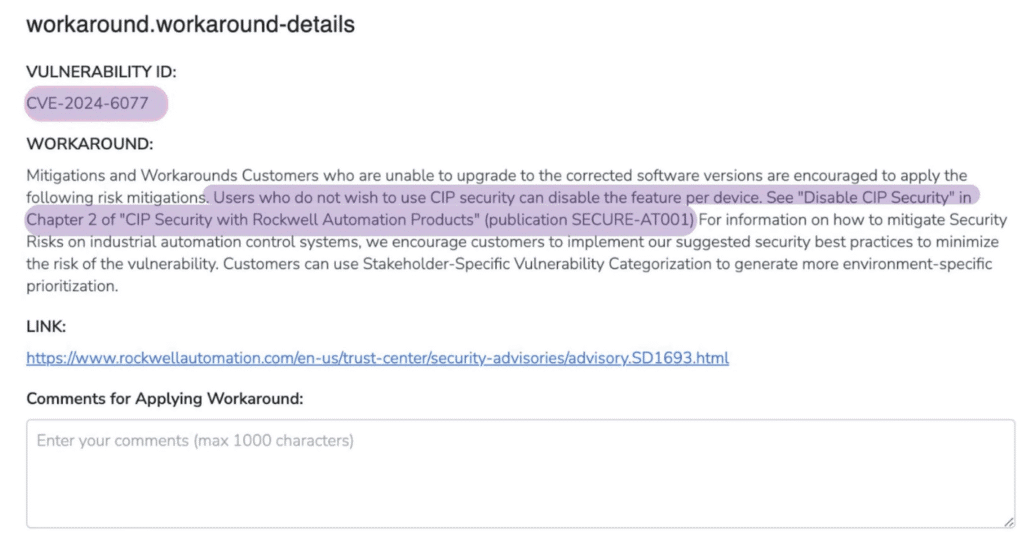
Platform View – Workarounds: For each identified vulnerability, Rockwell recommends limiting physical access and applying established cybersecurity best practices. In the case of CVE-2024-6077, the vendor-recommended workaround removes exposure when CIP security is disabled.
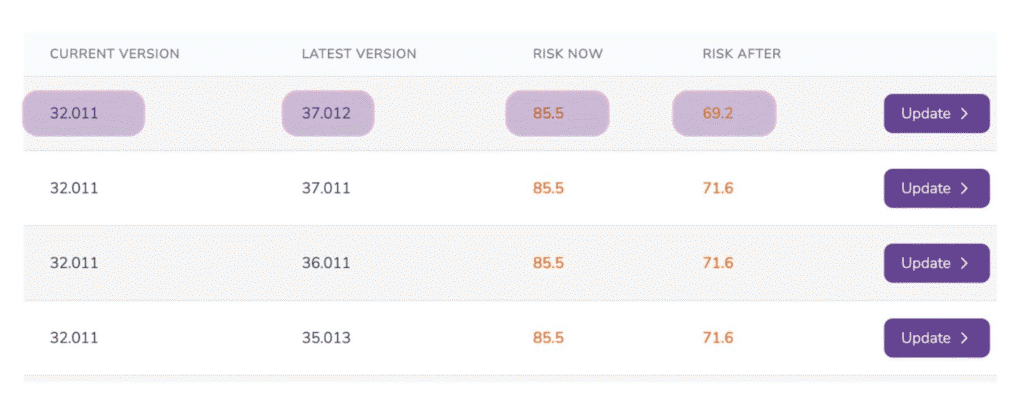
Platform View – Upgrade Path: For environments running firmware version 32.011, the most recent vendor release available is 37.012, which significantly lowers the associated risk score. CVE-2024-6077 is remediated by upgrading to firmware version 33.017 or later.
Outcome
With DeviceTotal in place, the security team achieved the following outcomes:
- Accurate identification of ControlLogix firmware version 32.011 as vulnerable
- Upgrade planning aligned with scheduled maintenance cycles
- Compliance preservation supported by vendor-validated evidence
- Removal of blind spots caused by inconsistencies across data sources
How DeviceTotal Integrates with Oil & Gas OT Security Teams
Asset Inventory Alignment
Fragmented inventories, including differing ControlLogix and GuardLogix classifications, are normalized to provide OT teams with a clear and accurate risk profile.
Compliance and Regulatory Reporting
Regulatory frameworks such as NERC CIP, IEC 62443, and NIS2 require vulnerability data verified by equipment vendors. DeviceTotal delivers audit-ready evidence directly linked to Rockwell advisories.
Incident Response Readiness
During active incidents, SOC and OT teams require firmware-specific intelligence to determine which controllers require isolation or patching. DeviceTotal provides this precision without disrupting production operations.
Lifecycle and Procurement Management
Given the 10- to 20-year operational lifecycles common in oil and gas environments, DeviceTotal tracks end-of-life and end-of-support milestones, along with vendor patch availability, to prevent long-term hidden exposure.
Why It Matters
At the scale typical of oil and gas operations, even minor discrepancies between vendor advisories and public vulnerability databases can lead to:
- False negatives that propagate across extensive asset inventories
- Compliance gaps where devices are reported as secure despite being exposed
- Escalating downtime costs when vulnerabilities remain undetected in critical systems
- Increased risk to operational safety and regulatory standing across production networks
DeviceTotal consolidates vendor intelligence and public vulnerability data into a single, authoritative source of truth.







