Author: Julia Grits, Netwrix Brand Manager
Artificial intelligence is rapidly becoming part of the daily workflow of development, DevOps, marketing, and business analytics teams. ChatGPT, Microsoft Copilot, Google Gemini, Claude, Grok, and other chatbots have become convenient assistants. However, along with the benefits, a new data leakage channel has emerged.
One careless copy-paste—and a piece of source code, an API key, or an internal document is already outside the controlled perimeter.
Netwrix Endpoint Protector extends the traditional DLP approach by enabling control over user interaction with AI web tools.
Let’s take a closer look.
The New DLP Reality: AI as a Data Leakage Channel
Traditionally, DLP focused on:
- USB storage devices
- cloud storage
- web uploads
However, the emergence of LLMs and chatbots has introduced a fundamentally new risk vector:
- entering sensitive data directly into chat text fields
- attaching files containing code, logs, or configurations
- using AI without understanding where data is sent or how it is processed
Netwrix Endpoint Protector addresses this challenge by extending Data Loss Prevention to AI chatbots.
What Netwrix Endpoint Protector Controls
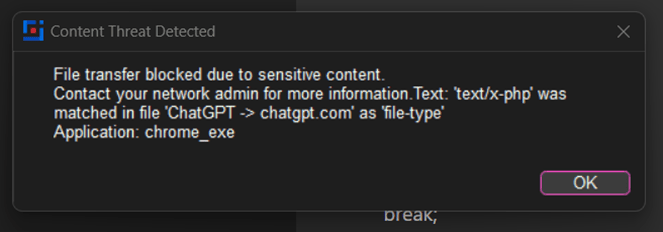
The CoreWin team reproduced a use case on a demo server involving sending PHP source code to the web version of ChatGPT.
DLP Policy Configuration:
- select the operating system where the policy applies
- define the action (block, report, etc.). In our case—block and notify the user
- exit points = web browsers
- select the “Source Code” category in blacklists (PHP in our example)
- apply the policy to objects (group, computer, user, or a computer + user combination)
- enable Deep Packet Inspection for this policy
- ensure the agent updates the policy—and start testing 🚀
Simulation: sending code as a prompt or file
1. Text Prompt Control (Paste / Typing)
Netwrix Endpoint Protector analyzes text that users type or paste into the ChatGPT web interface:
- source code
- confidential keys
- personal data
- internal information configured for blocking
This control works in real time—before the chatbot UI actually sends data to the server.
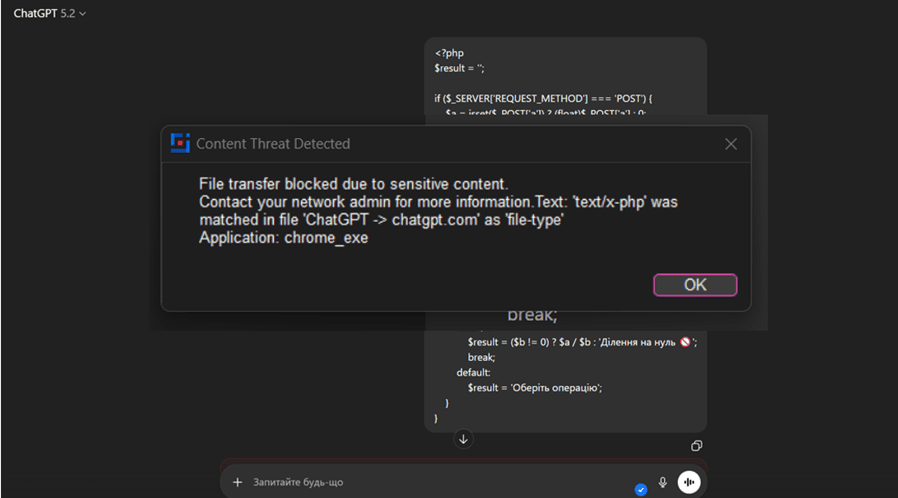
2. Attachment Control
DLP policies also apply to files that users attempt to:
upload to ChatGPT → attach to Copilot, Gemini, Claude, etc.
Netwrix Endpoint Protector can:
- block uploads containing sensitive content
- allow only specific file types
- log incidents for further investigation
How it works technically
The key control mechanism is Deep Packet Inspection (DPI).
DPI in the Context of Endpoint Protector
Deep Packet Inspection is a traffic analysis technology that enables:
- inspection of both headers and transmitted content
- identification of information types within encrypted HTTPS sessions
- enforcement of DLP policies at the content level rather than only by domain or application
For chatbots, DPI is used to:
- analyze text transmitted to the chat
- detect code patterns (source code, SQL, scripts)
- apply content-based rules to AI requests
Netwrix Endpoint Protector does not just “see ChatGPT”—it understands what is being sent.
This is not a simple keyword-based DLP.
Supported detection mechanisms include:
- Content Classification
- Pattern Matching (regex for API keys, tokens, credentials)
- Context-aware detection (code structure, syntax patterns such as function, class, import, SELECT, etc.)
- Fingerprinting / Exact Data Match
Incident Logging Includes:
- user
- endpoint
- application / URL
- content type
- action (blocked / monitored / allowed)
- timestamp
Events can be exported to SIEM and correlated with other DLP / EDR events.
Business Value for Organizations
Implementing DLP for LLM usage enables organizations to:
- reduce the risk of intellectual property leakage
- maintain security and compliance requirements
- allow AI usage without a complete ban, but under control
- gain full visibility into AI-related user activity
Conclusion
LLM-based chatbots are not a temporary trend—they represent a new working standard. The hype may fade, but usage will remain. Without control, they quickly become an invisible data leakage channel.
Netwrix Endpoint Protector provides a mature and practical approach:
- prompt control
- attachment control
- Deep Packet Inspection
- support for major AI platforms
This enables organizations to safely integrate AI into business processes without compromising security.







