Author: Julia Grits, Netwrix Brand Manager
Many companies, especially enterprise organizations with their own development resources, build internal products.
These can range from custom web portals and testing environments all the way to proprietary operating systems or even in-house cybersecurity solutions. For some organizations this helps save budget, for others it addresses vulnerability concerns. And sometimes it’s simply difficult to find off-the-shelf software that fits complex internal processes. In such cases, building your own solution can be a perfectly valid option.
But (there’s always a “but”) custom systems often fall outside the company’s security perimeter. Why?
Because, well… nobody raised their software project just to hear it’s not the best one. 😊
Jokes aside, such software is usually developed to solve very specific business tasks and is not always integrated with corporate cybersecurity or access management systems.
As a result, credentials for these systems may end up being stored in:
- Excel files
- corporate chat messages
- internal documentation
- employees’ personal password managers
This means they are stored without any centralized control, even if the main infrastructure already uses Privileged Access Management (PAM).
And that creates significant security risks.
Key risks of uncontrolled password storage
- lack of access control
- inability to clearly identify who has access to critical accounts
- difficulty revoking access quickly
- after an employee leaves or changes roles, updating all passwords can be complicated
- lack of auditability because credentials are used without oversight
Under these conditions, accountability and responsibility quickly disappear.
Centralized credential storage as an access management approach
Ideally, PAM with ephemeral accounts would be the best solution, but that’s not always feasible. Traditionally effective approach is using a centralized credential vault.
Such a solution allows organizations to:
- store credentials in encrypted storage
- control access through roles and policies
- maintain an audit trail of credential usage
- centrally update passwords
This approach is widely used in traditional PAM systems to protect privileged credentials.
Benefits of centralized access management
- Using a centralized vault significantly improves control over critical access.
- It reduces the risk of credential leaks, since passwords are no longer shared between employees in plain text.
- It also enables full access auditing, as all actions involving accounts can be recorded and used for internal control or compliance audits.
The solution we propose
Netwrix Password Secure enables centralized management of credentials across multiple systems, including internal or custom-built applications.
The solution functions as a secure credential vault and supports access to:
- RDP systems
- SSH servers
- web applications
- and more
With this approach, organizations can maintain a consistent access management model for both standard infrastructure and custom systems.
Solution advantages
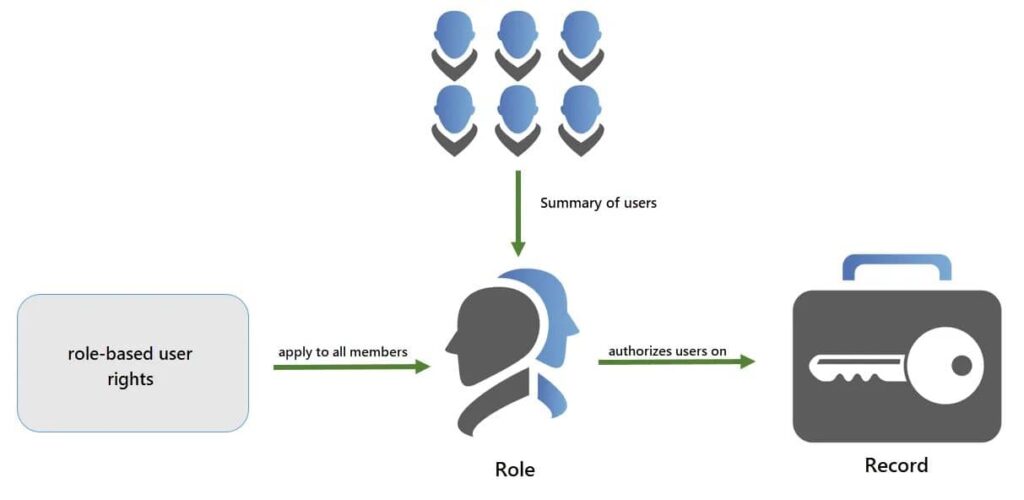
- Role-based access control ensures users only have access to what they actually need.
- Deployment is flexible: on-premises, in the cloud, or in a hybrid environment.
- The platform protects passwords using end-to-end encryption and multi-factor authentication. Each account is encrypted individually, while features such as password policies, approval workflows, and session recording help minimize the risk of credential compromise or misuse.
- Every password access, update, or sharing event is tracked. This helps organizations meet compliance requirements such as GDPR, HIPAA, NIS2, and others. Built-in reporting also makes audits significantly easier.
Conclusion
Internal and custom-built systems often remain outside standard access management frameworks. Yet these systems may store critically important business data.
Centralized credential management using solutions like Netwrix Password Secure allows organizations to bring such systems into a unified security framework and significantly reduce the risk of credential compromise.
If you’re interested in improving password policies and complexity requirements, we recommend reading this article from our library.







