A low-cost malicious gadget can compromise security within seconds. Devices such as BadUSB, Rubber Ducky, and Flipper Zero bypass traditional USB blocking by disguising themselves as keyboards and executing commands at machine speed. Netwrix Endpoint Management combines the device control capabilities of Netwrix Endpoint Protector with the privilege control policies of Netwrix Policy Manager to block harmful peripherals, eliminate unnecessary administrator rights, and limit the spread of an attack before it escalates into a major incident.
The following article outlines how these attacks operate, why conventional defenses fail, and how to prevent them effectively.
A Low-Cost Malicious Gadget Can Wreck an Entire Network
Consider a scenario in which a USB device is left in a parking area and later plugged in out of curiosity.
Within moments, the device impersonates a keyboard and issues hundreds of commands at extreme speed. It disables security protections, installs malicious software, and opens backdoors.
One connection is enough. One moment of carelessness. One low-cost gadget.
This scenario is not hypothetical. These attacks—referred to as BadUSB, Rubber Ducky, or Flipper Zero exploits—represent one of today’s most underestimated endpoint threats.
What Are BadUSB, Rubber Ducky, and Flipper Zero Attacks?
These attacks fall under HID (Human Interface Device) exploitation. The mechanism is simple yet highly destructive:
- They do not behave like storage devices. Instead of appearing as USB drives, they masquerade as keyboards.
- They operate far faster than a human could. Commands are injected at lightning speed before any intervention is possible.
- They exploit implicit trust. Operating systems accept them as legitimate keyboards, granting unrestricted input.
Anatomy of an Attack
USB HID exploits function much like sleight of hand—simple in appearance but extremely effective:
- Delivery: The attacker places the device where an employee might discover it or sends it through the mail.
- Execution: Once the device is connected, keystroke injection begins immediately.
- Privilege escalation: If the user has local administrator rights, the spoofed keyboard can disable security tools, execute malware, or create new accounts.
- Lateral movement: If administrative credentials are reused across endpoints, attackers can traverse systems quickly.
The outcome is clear: a compact device triggers a potentially devastating breach.
Why Traditional Defenses Fail
Most organizations block USB storage. However, blocking storage devices does not block HID peripherals. A BadUSB attack device does not register as storage; it presents itself as a new keyboard. For this reason, traditional controls overlook the threat, leaving a critical blind spot.
How Netwrix Prevents These Attacks
Netwrix Endpoint Protector: Device Control Against HID Threats
The Device Control module in Endpoint Protector enables real-time defense against unauthorized HID activity:
- Blocking additional keyboards: A simple policy prevents any unexpected keyboard-class device from functioning.
- Vendor ID allowlisting: Only trusted, recognized keyboards based on approved Vendor IDs are permitted to operate. Any device attempting to impersonate a keyboard without a matching vendor ID—such as Rubber Ducky or Flipper Zero—is rejected.
- Cross-platform enforcement: Alerts and blocks function consistently across Windows, macOS, and Linux.
The result is a low-maintenance but highly effective layer of defense against HID attacks.
Two-Step Netwrix Endpoint Protector Process:
Step 1: Deny access for additional keyboard devices.

Step 2: Apply Vendor ID allowlisting to ensure only approved keyboards operate, instantly blocking devices that fail verification.

Visual examples demonstrate how unintended devices are blocked across major operating systems.

Netwrix Policy Manager: A Second Layer of Defense
If attackers obtain physical or remote access, device control alone may not suffice. Netwrix Policy Manager (formerly PolicyPak) strengthens protection by enabling:
- Removal of default local administrator rights, reducing opportunities for privilege escalation.
- Just-in-time access workflows integrated with ServiceNow or other helpdesk systems for legitimate administrative requests.
- Restrictions on high-risk utilities such as PowerShell, CMD, and Run, while allowing approved scripts and applications.
- SecureRun™, which automatically blocks untrusted self-downloaded executables.
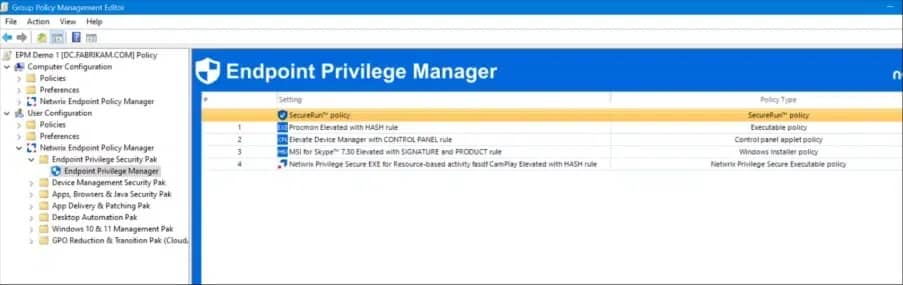
Together, these measures prevent attackers from leveraging rogue devices or compromised privileges. Creating Endpoint Privilege Management rules to bypass UAC prompts is straightforward.
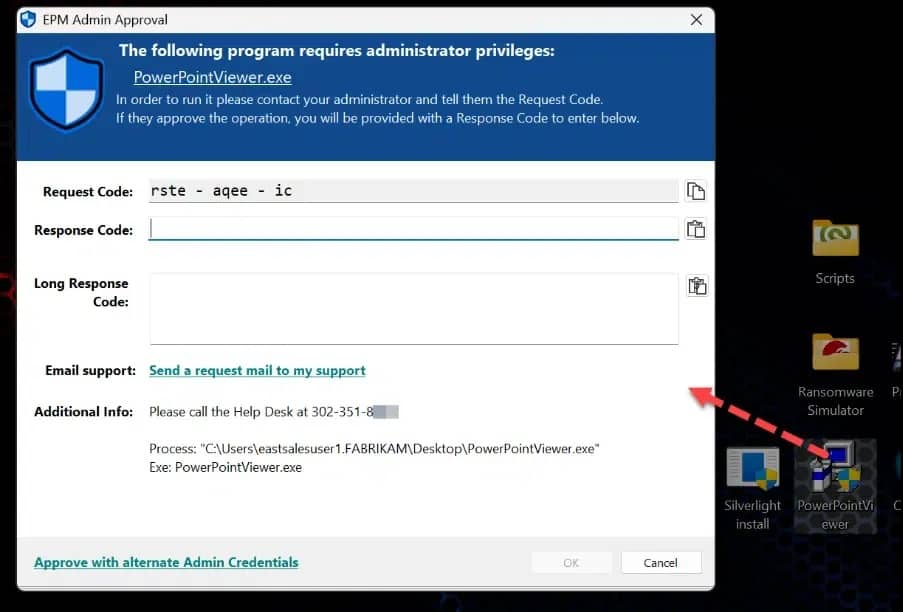
Items without predefined rules can be approved using just-in-time admin workflows.
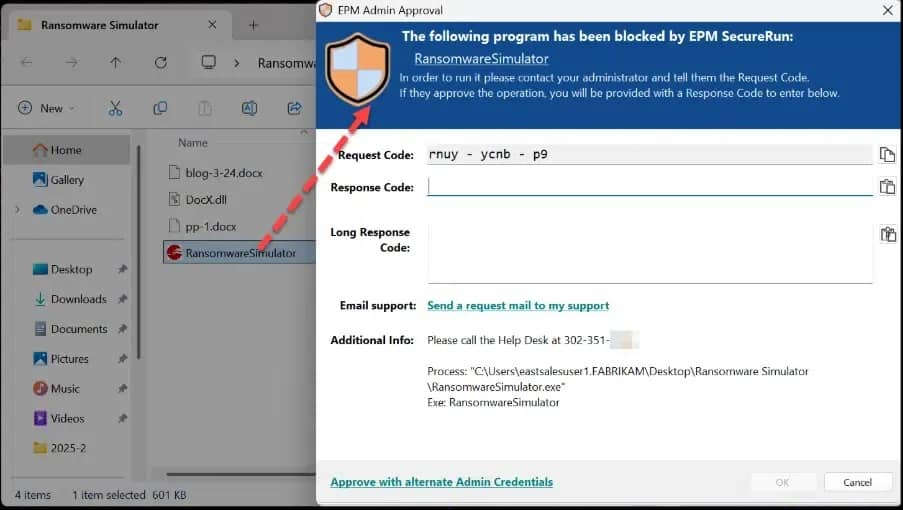
Applications blocked by SecureRun can be routed to the helpdesk for investigation.
Business Value for Security Leaders
Netwrix Endpoint Management—combining Endpoint Protector and Policy Manager—delivers security benefits that go beyond preventing malicious gadgets:
- Compliance alignment: Meets guidelines from NIST, CIS, and ISO for removable media and privilege control.
- Operational efficiency: Maintains user productivity by permitting trusted devices while blocking unauthorized hardware.
- Risk reduction: Detects and blocks lateral movement attempts before ransomware or similar threats propagate.
- Cost avoidance: Prevents costly incident response and operational downtime stemming from a single careless action.
Key Takeaway
BadUSB, Rubber Ducky, and Flipper Zero attacks target one of the most trusted components in any environment: the keyboard.
With Netwrix Endpoint Management—powered by Endpoint Protector and Policy Manager—organizations can:
- Block unauthorized USB HID devices before malicious commands execute.
- Eliminate redundant local administrator rights and enforce least-privilege principles.
- Contain lateral movement using just-in-time access and privileged session controls.
The result: a high-risk attack vector becomes negligible, and a low-cost malicious gadget no longer carries the potential to create a multimillion-dollar incident.







