Author: Andrew Mikhaliuk, CEO of CoreWin
The modern digital world, especially in our realities, has become much less secure. Threats can lurk not only in well-known risk areas (such as torrent forums, pornographic websites, spam, or phishing emails), but also in safe areas.
Attackers are increasingly using the Google Ads platform to distribute malware to unsuspecting users who are searching for popular software products.
Among the products imitated in these campaigns are Grammarly, MSI Afterburner, Slack, Dashlane, Malwarebytes, Audacity, μTorrent, OBS, Ring, AnyDesk, LibreOffice, TeamViewer, Thunderbird, and Brave.
Attackers clone the official websites of the above projects and distribute Trojan versions of the software when users click the download button.
Of course, the best protection recommendation is to use specialized attack detection and response systems, also known as XDR, and incident collection and aggregation systems (SIEM) if you have a large infrastructure. However, for critical infrastructure, as well as for conducting an investigation on an infected “patient,” this may not be enough. As the saying goes: if you want to do something well, do it yourself.
In this post, I’d like to share a methodology that I consider to be one of the most versatile and effective: analyzing the system’s RAM. The disadvantage of this approach is that to detect a threat, it must be active, i.e., the system must be actively infected. The advantages, I think, will become apparent in the course of developing such a methodology. Note: this instruction is described for Windows systems, for Linux the tools may differ, although the methodology will remain the same.
Step 1. Preparation
First, you need to prepare and install free tools for the job:
- DumpIt, a RAM dump collection tool
- Volatility, an incident analysis and investigation tool with a graphical interface
- runs on Python, so you need to install it as well
Step 2. Collecting information
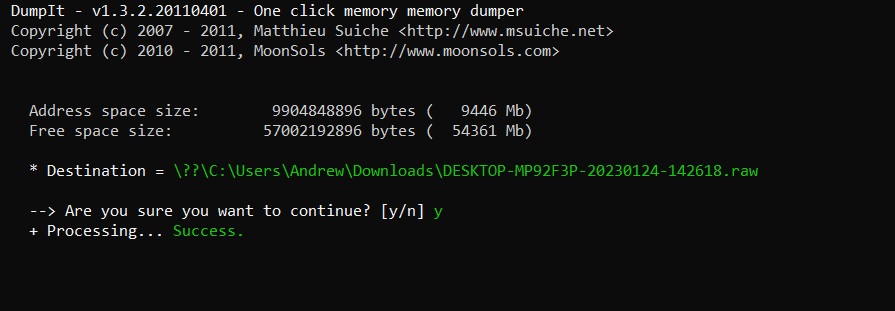
We have to collect a memory dump, so let’s use DumpIt. The interface is simple (a text console), but to collect it, you just have to press two buttons, first “Y” and then “Enter”. Be prepared for the fact that the dump will be massive, on my machine it weighed more than 9 GB.
Thus, if an attacker has infected you or is even actively “operating” remotely right now, the system will execute processes using RAM, and thus we will see them in this “photo” of RAM.
Step 3. Example
In real life, we could continue to use it, but since my machine is clean and free of infections, we’ll use this file for an example.
Step 4. Installing the Volatility WorkBench
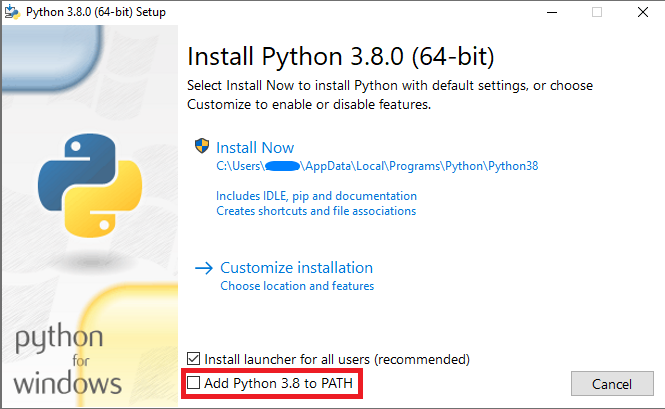
First, let’s install Python. Everything is simple: download the latest stable release from the website and run the installer. Important: at the last step, do not forget to update the PATH.
Unzip the archive and run VolatilityWorkbench.exe
In the interface, find the created memory dump and run Get Process List.
As soon as the system performs the initial analysis, we are ready for the most interesting part.
The initial results of the analysis, my results, are below.

At first glance, everything looks quite clean, but we have a tool at our disposal that exists to search for memory injections.
In the command menu, select windows.Malfind.

It is a tool that looks at the binary code of a process and searches for suspicious signatures in the executable binary code. If we go a little deeper into the methodology, the malfind command helps to find hidden or in-memory code or DLLs based on characteristics such as the VAD tag and permissions.
As a result, we were able to find a list of processes that are suspicious and need to be investigated.

The first thing you should pay attention to is the process itself. Does it look reliable? What are its properties on the machine? Some processes can be identified immediately.
It may also be that the process itself is legitimate, but it is infected, and the attacker uses it for their computations. So sometimes the list contains seemingly familiar processes, but this does not guarantee that the tool has been falsely triggered. It just means that the situation requires further study.
Now it’s clear that we should dig further, but the Volatility WorkBench toolkit is limited, so we need to upgrade to the latest version with a command line.
Step 1. Preparation
First, you need to prepare and install free tools for your work:
- Volatility, an incident analysis and investigation tool
- runs on Python, so you have to install it as well (or have it installed from the previous step)
- Git for Windows is also required for Windows
- and also Visual Studio C++ Build Tools
Step 2. Set the Volatility
Mentally prepare yourself – this is the step that requires the most endurance.
First, install Python (described above in this article).
Next, Git for Windows. It is also a simple installer. You can safely leave the default values when the installer asks you something (and it will ask you a lot). The only thing I’d like to point out is the text editor, which is VIM by default. I recommend choosing the one you use (for me, it’s either Notepad++ or Sublime).
Next, we install C++ Build Tools. This is one of the few native tools for Windows. You can trust it and simply follow the “next-next-next…done” approach.
Now, finally, it’s time to get to Volatility. Go to the project’s GitHub page and copy the link to the code.

Log in to PowerShell as administrator and go to the directory where Volatility will be located (for me, it’s C:\Volatility).

Here we use the previously installed git and clone the branch to the directory with the git clone command – the previously copied address is

Now we need to install the very finicky python snappy library on Windows. Accordingly, in my case, I need the 64-bit version of python_snappy 0.6.1 cp311 cp311 win_amd64.whl
Now we install the library. pip install – file path

Great! Anyone who has ever tried to install this library on Windows will understand how pleasant this message is.
Go to the volatility3 directory created during cloning.

Go to the requirements.txt file. Change the version of python-snappy==0.6.0 to python-snappy==0.6.1 | since this is the version we installed earlier.
Install all the dependencies, i.e., the libraries that are essential for functioning. Fortunately, the list of all dependencies is already available, so we enter the following command: pip install -r .\requirements.txt

Now (finally) check if volatility is working with the command python vol.py -v

Back to the analysis
To analyze the dump file, you need to open it with the following command: python vol.py -f [file path and name] [platform]. [module].
We are currently interested in whether there is any suspicious network communication to identify whether an attacker is connecting to the machine.
Let’s run the command: python vol.py -f C:\Laboratory\WinDump.mem windows.netstat
We have interesting results:

A few open connections. Let’s take a look at where these IPs are located.
Here, you can use online IP lookup services. I usually use ip2location. While most of the connections are from the US (where the subject is presumably located), there’s a very unusual connection from Mexico.
And that’s it?
Of course not. We have just touched on the possibilities of such a simple laboratory for studying memory dumps. There are actually plenty of tools. And the main thing is that this open-source software is currently being actively supported and updated.
One of the key elements of investigating cyber incidents on a computer or a network of computers is the correct acquisition and analysis of RAM. According to international practice, this is one of the main tools for obtaining evidence of illegal actions on a workstation.
I hope that the tools described above will be useful to you, and most importantly, will be an incentive to delve deeper into the topic of incident investigation.







