Traditionally, the IBM and Ponemon Institute Cost of a Data Breach Report 2025 reflects new technologies, new tactics, and the latest developments. The new global study shows how artificial intelligence is significantly outpacing security and management in favor of immediate implementation. The results indicate that unmanaged artificial intelligence systems are more likely to experience breaches, and their cost in case of a compromise is higher.
Highlights from the 2025 IBM Cost of a Data Breach Report
- For the first time in five years, the worldwide average cost of a data breach dropped—reaching $4.44 million (a 9% decrease compared to 2024)—primarily due to faster incident detection and containment, driven in large part by the adoption of AI and automation.
- In the United States, on the contrary, there was a record increase to $10.22 million (+9%) due to higher fines and rising detection costs.
Artificial intelligence as a new risk
- Thirteen percent of organizations disclosed breaches linked to their AI models or applications, and 97% of those cases lacked adequate access control measures.
- Shadow AI has become one of the three largest factors increasing the cost of an incident: +$670K to the average damage.
Most expensive attack vectors
- Malicious insiders – $4.92 million.
- Supplier/supply chain compromise – $4.91 million.
- Most common vector – phishing (16%), $4.8 million.
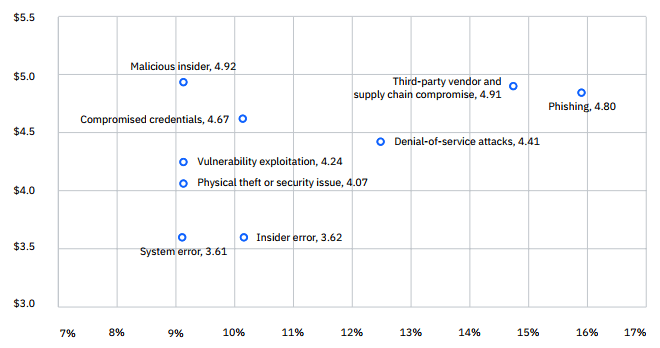
Percentage of all data breach cases (measured in millions of US dollars), 2025
Impact of AI and automation on cost reduction
- Organizations with extensive AI/automation deployment saved an average of $1.9 million and reduced detection/containment time by 80 days.
- The cost of an incident without AI/automation – $5.52 million, with extensive implementation – $3.62 million.
Data distribution
- Malicious actors most often deliberately targeted customers’ personally identifiable information (PII) – 53%, costing $160 per record; intellectual property (IP) was the most expensive type of data ($178 per record).
- Data storage in multi-environment setups had the most expensive incidents ($5.05 million) and the longest remediation time (276 days).
Recovery after an incident
- Only 35% of organizations fully recovered; 65% are still in the process.
- 76% of those that recovered spent more than 100 days doing so.
- The share of organizations stating they would pass on breach-related costs to customers decreased by almost one-third to 45% in this year’s report, compared to 63% last year. However, about one-third said they would raise prices by more than 15%.
Regulatory fines
- 32% of cases resulted in fines; 48% of fines exceeded $100K, with the highest amounts in the United States.
Key factors influencing incident costs
Top 5 cost reducers:
- DevSecOps (–$227K)
- AI and machine learning insights (–$223K)
- SIEM (–$212K)
- Threat intelligence (–$211.9K)
- Encryption (–$208K)
Top 5 cost increasers:
- Supply chain attacks (+$227K)
- Security system complexity (+$208K)
- Shadow AI (+$200K)
- AI tool deployment (+$193K)
- Impact on IoT and OT environments (+$175K)







