The cybersecurity landscape is rich with specialized tools tailored to specific functions. Among these, vulnerability scanners and Security Information and Event Management (SIEM) systems stand out as essential components of any mature security framework. While both are critical, they serve fundamentally different purposes. A clear understanding of their roles, capabilities, and how they complement each other is key to building an effective AppSec strategy.
Understanding Vulnerability Scanners
A vulnerability scanner functions as a proactive security tool aimed at uncovering potential weaknesses across digital environments. Depending on the scanner’s focus, it can assess systems, networks, or applications to uncover misconfigurations, exposed components, and known vulnerabilities. Some scanners operate passively, while others actively simulate attack vectors to provide actionable insights, typically ranked by severity and likelihood of exploitation.
Categories of Vulnerability Scanners
Scanners are typically grouped based on the assets they assess:
1. Application vulnerability scanners focus on software layers and include tools such as:
- DAST (Dynamic Application Security Testing): Tests running applications externally, identifying real-time vulnerabilities.
- SAST (Static Application Security Testing): Performs analysis of application source code to identify potential vulnerabilities.
Examples:
- Invicti: A comprehensive platform combining DAST with SAST, SCA, and API testing; its DAST engine verifies exploitability across layers.
- Acunetix: Known for its high-speed scanning and proof-based detection.
2. Network vulnerability scanners evaluate infrastructure-level components.
Common Vulnerabilities Detected
Each scanner targets different vectors based on its scope.
Application Layer (DAST Tools):
- SQL Injection: Executes unauthorized SQL commands via user inputs.
- Cross-Site Scripting (XSS): Injects scripts into users’ browsers, often to steal session tokens.
- Command Injection: Sends malicious system commands for execution by the server.
- Directory Traversal: Grants access to unauthorized files via manipulated file paths.
- Security Misconfigurations: Covers weak HTTP headers, verbose error messages, and exposed config files.
Network Layer (Infrastructure Scanners):
- Open Ports: Unrestricted access points that may expose services unnecessarily.
- Weak Encryption: Outdated SSL/TLS versions and vulnerable cipher suites.
- Unpatched Services: Known exploits in software or OS components.
- Default Credentials: Pre-configured logins easily targeted by attackers.
- DNS Cache Poisoning: Spoofed or redirected DNS queries due to misconfigurations.
Real-World Exploit Case
In 2017, the Equifax data breach exposed personal data of millions due to an unpatched Apache Struts flaw—a vulnerability that modern DAST tools could have flagged, enabling early remediation and likely avoiding the breach altogether.
What is a SIEM?
Security Information and Event Management (SIEM) platforms collect, analyze, and correlate logs from various IT components. Their role is reactive: detecting, alerting, and reporting suspicious activity across the environment in real time, while aiding compliance and investigation.
Key Functions of SIEM
- Log Aggregation: Collects data from systems, applications, and network devices.
- Event Correlation: Detects patterns and anomalies across disparate data.
- Real-Time Alerts & Reports: Provides immediate notifications and forensic reports for incident response.
Examples of Threats Detected by SIEM
- Insider Threats: Suspicious access behavior from internal actors.
- Advanced Persistent Threats (APTs): Stealthy, long-term intrusions.
- Malware Activity: Detects command-and-control signals or malicious binaries.
Real-Life SIEM Detection
A financial firm uncovered unauthorized internal access to client data. Their SIEM identified abnormal access times and flagged the activity, enabling rapid containment before data was exfiltrated.
Core Differences Between Vulnerability Scanners and SIEM
| Vulnerability Scanners | SIEM | |
| Main Objective | Identify weaknesses before they are exploited | Monitor, correlate, and respond to incidents in real time |
| Data Sources | Scans systems and applications | Aggregates logs from IT infrastructure |
| Approach | Proactive, scheduled or on-demand | Reactive, continuous monitoring |
| Output | Detailed vulnerability reports with fix suggestions | Live alerts, dashboards, compliance logs |
| Response Actions | Offers guidance for manual remediation | Can initiate automated mitigations |
Why Use Both?
A layered approach combining both solutions is more effective:
- Proactive Defense: Scanners identify risk before it’s exploited.
- Ongoing Surveillance: SIEMs (like Wazuh) monitor for signs of exploitation or compromise.
- Improved Correlation: Data from scans can be leveraged to refine SIEM correlation logic, enhancing the accuracy of threat detection.
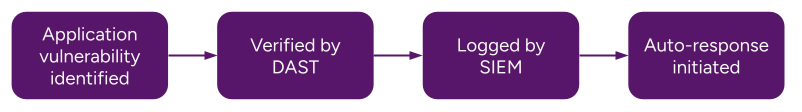
The following flowchart illustrates how the processes of vulnerability identification and threat detection converge within a unified workflow:
Why DAST Bridges the Gap
While scanners and SIEMs are each valuable, they often operate independently. One flags risk, the other reacts. What’s often absent is confirmation – clear evidence that a detected vulnerability can actually be exploited. That’s where DAST comes in.
Dynamic Application Security Testing fills the validation gap. Platforms like Invicti, with proof-based scanning, confirm exploitability and eliminate false positives. This accelerates triage, improves focus, and enables confident remediation.
Unlike SIEMs that act post-breach or scanners that flag theoretical issues, DAST directly proves which flaws pose actual danger – delivering precise, fast, and relevant results.
Final Takeaway
Grasping the distinctions and synergies between vulnerability scanners and SIEM tools enables organizations to craft a more resilient security architecture – one that blends prevention with detection.
Security is not about seeing everything. It’s about identifying what’s real and acting on it. Adopting a DAST-first approach provides clear visibility into risk, validates exploitability, and facilitates remediation before any harm is done. When paired with the real-time visibility of SIEMs, it builds a security foundation that’s both proactive and responsive.







