IT systems audit
Netwrix Auditor
Netwrix is a company specializing in cybersecurity software. More than 13,000 organizations worldwide are already using Netwrix solutions. Founded in 2006, the company has received more than 150 industry awards and has been included in the Inc. 5000 and Deloitte Technology Fast 500 lists. The company is headquartered in Texas, USA.
Netwrix Auditor is a solution for auditing various systems in the context of security. For example, Active Directory, SQL Server, network devices, etc.

Get Netwrix Auditor Demo
Netwrix Auditor
More and more organizations, regardless of size or industry, are recognizing the value of conducting regular internal and external IT audits. There are many benefits: IT audits can help improve security, pass regulatory compliance audits, and optimize IT operations. But too often, the process is cumbersome and time-consuming.
Netwrix Auditor helps you improve security, facilitate audits, and achieve your goals with much less effort.
Minimize IT risks and proactively detect threats
Reduce risks to critical assets by identifying key gaps in data and infrastructure security and identifying forgotten and unauthorized permissions. Ability to customize the necessary security alerts with further defined automatic actions.
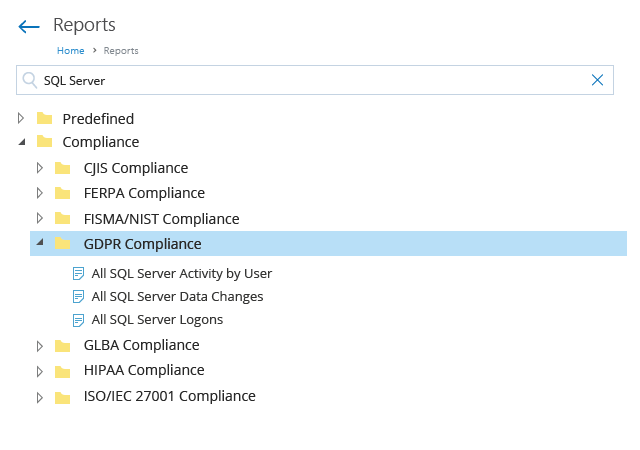
Ready-made reports on compliance with regulatory requirements
Reduce the time required to prepare for inspections by up to 85% with predefined reports that comply with common regulations and industry standards. Convenient search will help you find the reports you need in a few clicks and provide them to auditors.
Optimization of IT teams’ workflow
A steady stream of ad hoc tasks, such as user problem resolution requests or report generation, can distract IT teams from their core task of keeping systems available, so users can be productive. Netwrix Auditor monitors what is happening in the IT environment so that IT teams can proactively prevent issues and optimizes other IT tasks, such as automatically sending reports to stakeholders.
Centralized platform for auditing critical IT systems
Often, security teams find it difficult to work with different audit and reporting tools. After all, they need to collect information from all on-premises and cloud-based systems. Netwrix Auditor simplifies this process by supporting various IT systems, including Active Directory, Windows Server, Oracle Database, and network devices.
- Active Directory
- Microsoft Entra ID
- Microsoft 365
- Exchange
- SharePoint
- Nutanix Files
- Windows File Servers
- NetApp
- Dell Data Storage
- Oracle Database
- SQL Server
- Windows Server
- Network devices
- VMware
Main capabilities

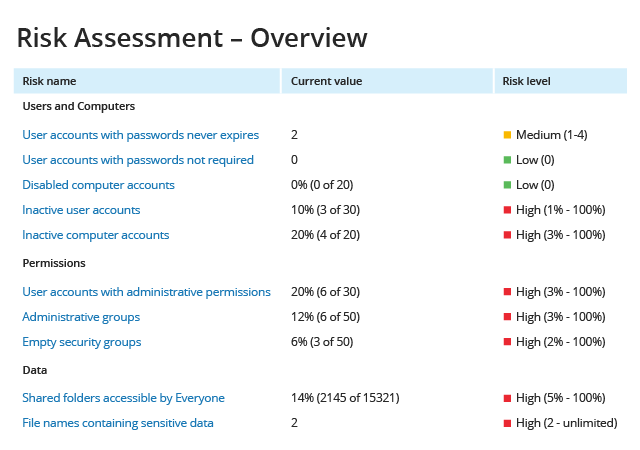
Risk assessment
Identify gaps in data and infrastructure security, such as numerous directly assigned permissions or too many inactive users. Thereafter, the security team will be able to adjust these permissions, which will significantly reduce the attack surface.

Protection of sensitive data
It’s important to protect your most critical assets. The first step is to identify sensitive data in the IT ecosystem. Then, regular checks on who has access to them and tracking activity around them (requires integration with Netwrix Data Classification).

Detailed reports
Comprehensive reports that contain all the necessary information for both the company’s management and auditors or other controlling authorities.
Optimization of user access
Adherence to the principle of least privilege by delegating access control to data owners.

Threat alerts
Instant alerts for suspicious activity around sensitive data so that IT teams can respond quickly and protect the company from system failures or regulatory fines.
Detecting sophisticated threats
Identify malicious insiders and compromised accounts through a comprehensive view of all anomalous activity alerts initiated by individuals, along with an associated aggregate user risk score.

Detect even minor signs of threats
Detect even subtle signs of possible threats, such as unusual account logins that may indicate account hacking or administrator activity after hours, so that measures can be taken before malicious actors take control of the system.

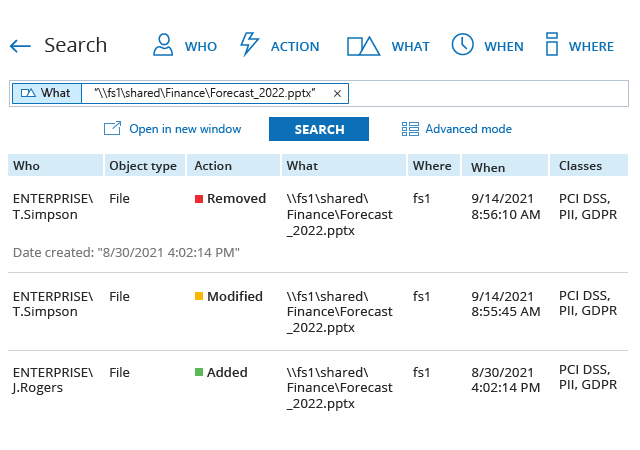
Convenient search
Get all the details you need in a few clicks, such as all access events for a user or all activities related to a specific sensitive file. This helps in investigating possible security incidents, resolving user issues, and preparing answers to special questions from auditors.

Compliance with the requirements
Ready-made reports including PCI DSS, HIPAA, SOX, GDPR, GLBA, FISMA/NIST, CJIS, etc.